Ubuntu
for confidential compute
Protect your data in use,
across public and private clouds.

What is confidential computing?
Confidential computing is a new security technique that protects virtual machine workloads from unauthorized access by keeping data encrypted while in system memory. This encryption shields sensitive code and data at runtime from privileged system software and other VMs by operating within a hardware-protected Trusted Execution Environment.
Benefits of Ubuntu for confidential computing
- Protect sensitive data by encrypting it when it’s being processed
- Secure your workloads in untrusted environments
- Build data clean rooms for collaborative AI analytics
AMD SEV SNP is available for both the host and guest
Ubuntu now supports AMD SEV-SNP on virtualization hosts, thanks to its kernel 6.14 and QEMU 9.2. This will be key to enable enterprises to deploy confidential VMs in on-premise data centers using Ubuntu as both the host and guest operating system.
Intel TDX is available on Ubuntu for both the host and guest
Ubuntu now supports Intel’s latest confidential computing technology. This hardware-based trusted execution environment enables you to add an extra layer of protection to the code and data running within your confidential virtual machines.
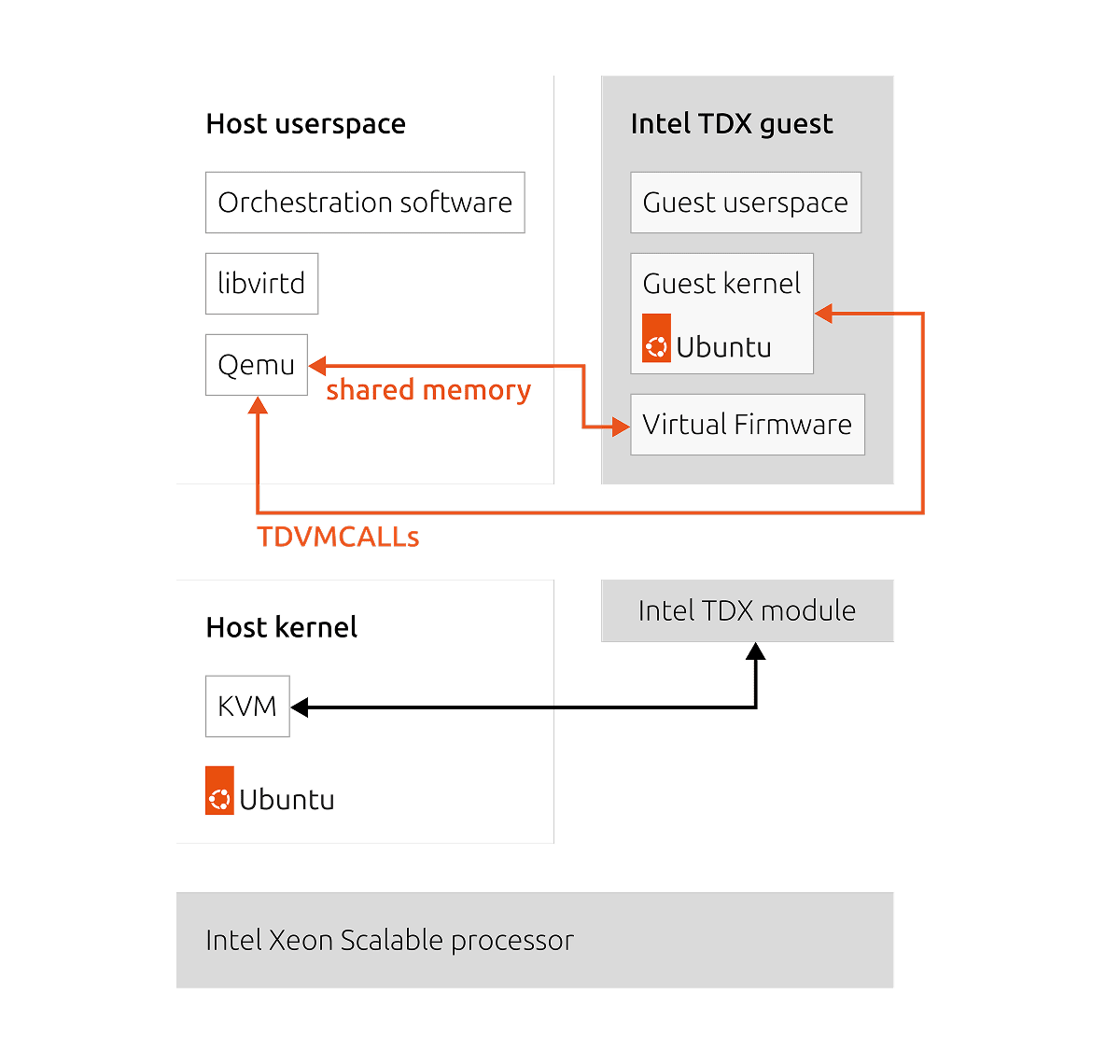
Private preview available on Ubuntu 25.04
Canonical’s strategic partnership with Intel gives you a customized Ubuntu build for Intel®TDX, incorporating all the latest necessary end-to-end host-to-guest patches available, even before they make it upstream.
Host side
We support a 6.8 kernel, derived from the 25.04 generic kernel, and offer essential user space components accessible through PPAs or QEMU 9.0. We also offer a set of user-friendly scripts to simplify the creation of confidential environments with just a few commands.
Guest side
We support a comprehensive package, featuring a 6.8 kernel, Shim, Grub, and TDVF, which serves as an in-guest VM firmware.
How confidential VMs work
Confidential VMs introduce a new trust boundary which only includes the software running within, and the platform’s hardware. All other software outside is no longer part of your trusted computing base. To provide such strong security guarantees, confidential computing relies on two main primitives:
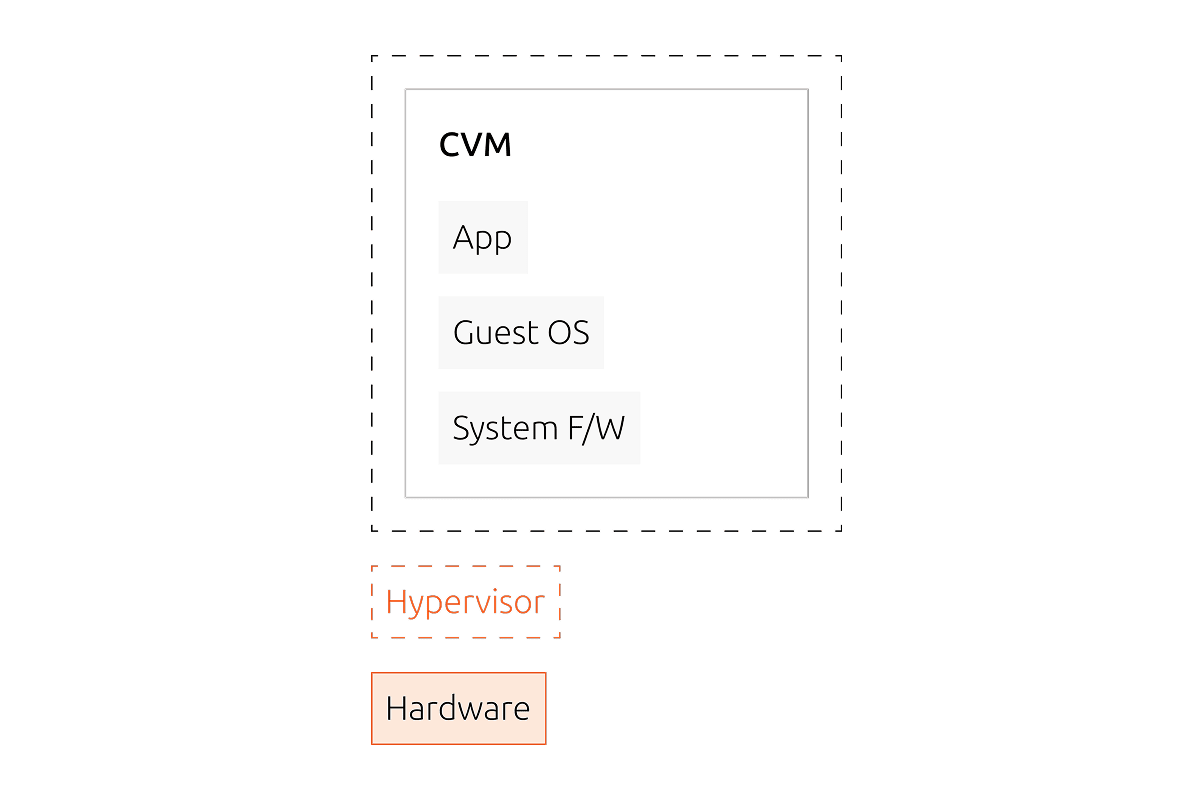
-
Isolation
Confidential computing capable CPUs are equipped with an AES hardware memory encryption engine, which encrypts data when it is written to system memory, and decrypts it when read. The encryption key itself is stored in the hardware root of trust and is never exposed to the platform’s system software.
-
Remote attestation
When a confidential VM is launched, its integrity is verified and its initial code and data are measured by a hardware root of trust. This ensures they have not been tampered with. The measurement is cryptographically signed and can be attested to a remote verifier.
Launch enterprise-grade confidential VMs on all major public clouds
How to map security primitives
to attacker capabilities
Uncover the details of Ubuntu’s security solutions and learn how to tailor them to your environment. Equip yourself with the tools to protect your data and stay one step ahead of evolving threats.
Use Ubuntu Pro to further harden your confidential VMs
While confidential VMs safeguard your workload from external threats, internal vulnerabilities within their boundaries can still pose risks. This is where Ubuntu Pro proves invaluable, ensuring your guest CVM software stack is continuously patched and up-to-date with up to 15 years of timely patches for vulnerabilities. Ubuntu Pro has been widely used to enable easy compliance with common regulatory frameworks including FIPS 140, DISA-STIG, CIS, FedRAMP, CMMC, PCI-DSS, Cyber Essentials, and more.
A solid foundation of your zero trust strategy
With confidential computing, you can remove the privileged systems software from your trusted computing base, reduce your attack surface, and get a remotely verifiable cryptographic guarantee before trusting any platform with your data.

Confidential computing in your private data center
Combine good data governance practices with the latest advances in privacy-enhancing computation. Use confidential computing to protect the confidentiality and integrity of the sensitive data hosted on your on-premises servers, using hardware-rooted primitives beyond traditional measures.
