
DISA-STIG on Ubuntu
Comply with the DISA Security
Technical Implementation Guide
Security Technical Implementation Guides (STIG) are developed by the Defense Information System Agency (DISA) for the U.S. Department of Defense (DoD). Ubuntu Pro has the necessary certifications and controls to comply with DISA-STIG guidelines on Linux, available on-premise or on public cloud.

How does Ubuntu enable your compliance with FIPS,
and DISA-STIG?
Learn about the US government security standards and the common challenges faced by organizations in their implementation. See how the Ubuntu Security Guide can transform systems compliance in a few minutes. Get to know how Ubuntu is a secure platform for government agencies and complying organizations to build, operate and innovate with open source applications and technologies.
What is DISA-STIG?
The Defense Information System Agency (DISA) is a US Department of Defense combat support agency. It provides and operates information infrastructure to support military operations and national-level leadership. The Security Technical Implementation Guide (STIG) is a configuration standard consisting of guidelines for hardening systems to improve a system’s security posture. It can be seen as a checklist for securing protocols, services, or servers to improve the overall security by reducing the attack surface.

DISA-STIG for Ubuntu
Together with Canonical, DISA has developed STIGs for Ubuntu. The U.S. DoD provides the STIG checklist, which can be viewed using STIG viewer, and SCAP content for auditing. The versions of Ubuntu that have STIGs available by DISA are marked on the table below.
DISA Security Technical Implementation Guides (STIGs) and Supplemental Automation Content for Ubuntu
-
Ubuntu 16.04 LTSConfiguration guide
-
Ubuntu 18.04 LTSConfiguration guide
-
Ubuntu 20.04 LTSTooling and automation
-
Ubuntu 22.04 LTSTooling and automation
How to audit and comply
with DISA-STIG?
-
Auditing
Using the Ubuntu Security Guide for auditing is as simple as:
sudo usg audit disa_stigand get the report in machine readable or browser friendly format.
-
Compliance
Using the Ubuntu Security Guide for applying the necessary rules for compliance is as simple as:
sudo usg fix disa_stig
Canonical is offering
Expanded Security Maintenance
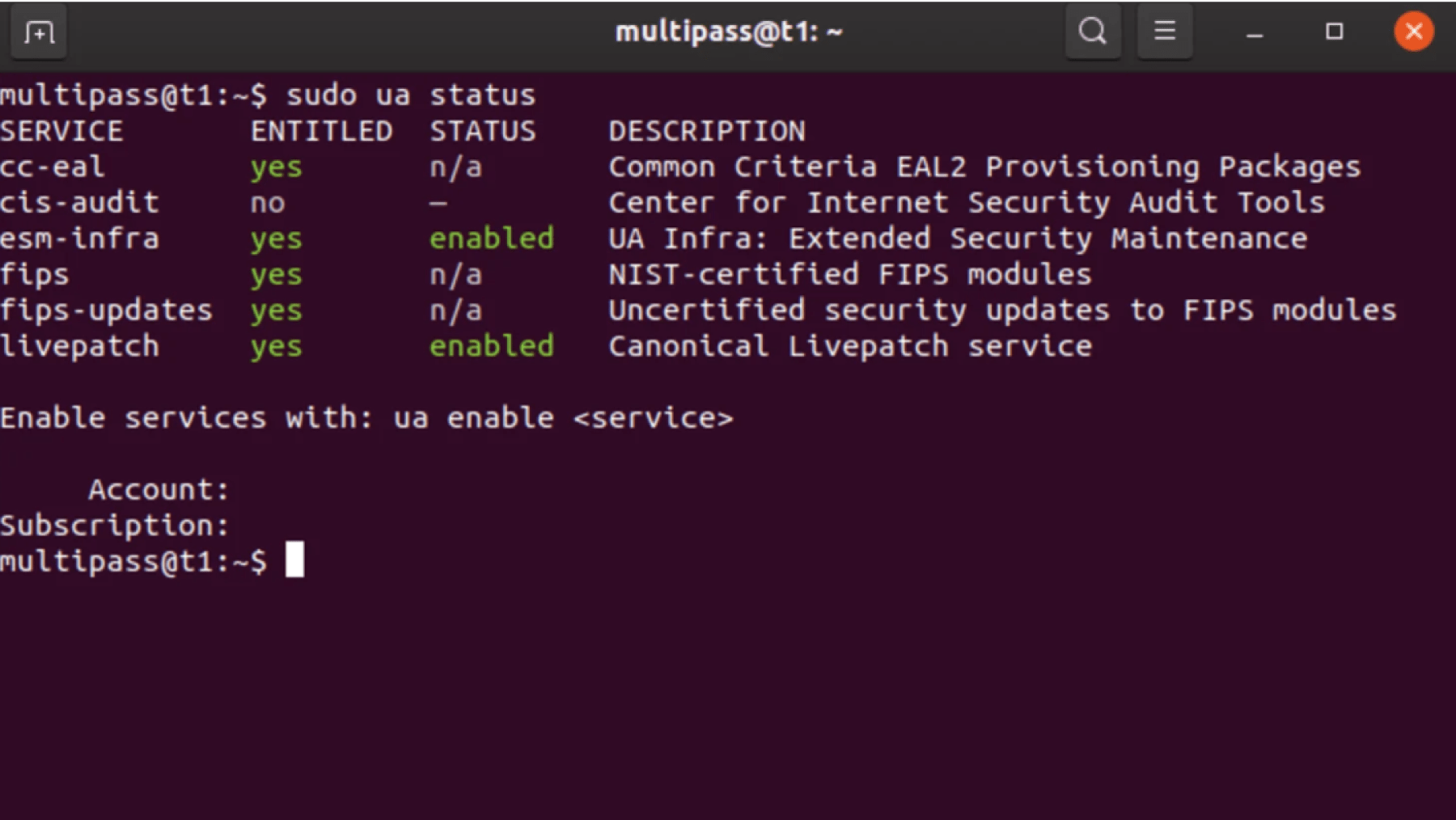
Canonical is offering Ubuntu Expanded Security Maintenance (ESM) for security fixes and essential packages.
Resources
Join the discussion
Further reading
- A comprehensive guide to NIS2 Compliance: Part 1 – Understanding NIS2 and its scope
- Rsync remote code execution and related vulnerability fixes available
- Needrestart local privilege escalation vulnerability fixes available
- Imagining the future of Cybersecurity
- 6 facts for CentOS users who are holding on
